Threats and vulnerabilities
Keeping up with the latest threats and vulnerabilities is a battle for any security pro. Get up-to-date information on email threats, nation-state attacks, phishing techniques, ransomware and malware, DDoS attacks, APTs, application vulnerabilities, zero-day exploits, malicious insiders and more.
Top Stories
-
Opinion
06 Dec 2023

How organizations can learn from cloud security breaches
Research shed light on cloud security breaches. It's time to learn from the past and mitigate these attacks in the future with strong cloud security and posture management. Continue Reading
-
News
06 Dec 2023

Forescout uncovers 21 Sierra Wireless router vulnerabilities
Forescout is urging enterprises to patch software for affected OT/IoT routers as attackers increasingly target edge devices to gain network access to critical infrastructure. Continue Reading
-
News
04 Dec 2023

Fancy Bear hackers still exploiting Microsoft Exchange flaw
Microsoft and Polish Cyber Command warned enterprises that Russian nation-state hackers are exploiting CVE-2023-23397 to gain privileged access to Exchange email accounts. Continue Reading
-
Feature
04 Dec 2023

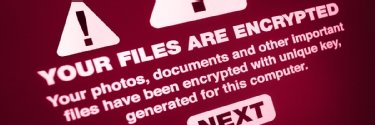
Top 13 ransomware targets in 2024 and beyond
Two in three organizations suffered ransomware attacks in a single year, according to recent research. And, while some sectors bear the brunt, no one is safe. Continue Reading
-
News
30 Nov 2023

Black Basta ransomware payments exceed $100M since 2022
Insurance provider Corvus and blockchain analytics vendor Elliptic partnered to examine how much damage the Black Basta ransomware group has caused in less than two years. Continue Reading
-
News
27 Nov 2023

Threat actors targeting critical OwnCloud vulnerability
Researchers observed exploitation attempts against a vulnerability affecting OwnCloud's Graph API app, highlighting threat actors' continued focus on file-sharing products. Continue Reading
-
Tip
22 Nov 2023

4 data loss examples keeping backup admins up at night
Protecting data is a critical task for backup admins, and threats are ever evolving. Preparation is key to preventing data loss and recovering quickly. Continue Reading
-
News
21 Nov 2023

CISA, FBI warn of LockBit attacks on Citrix Bleed
The latest advisory on exploitation of the Citrix Bleed vulnerability confirmed that the LockBit ransomware group perpetrated the attack on Boeing. Continue Reading
-
News
16 Nov 2023

Alphv ransomware gang claims it reported MeridianLink to SEC
MeridianLink said it recently identified a "cybersecurity incident," but the Alphv ransomware gang claims it breached the company and compromised customer data. Continue Reading
-
News
15 Nov 2023

VMware discloses critical, unpatched Cloud Director bug
A manual workaround is currently available for a critical VMware Cloud Director Appliance flaw, tracked as CVE-2023-34060, but no patch is available at press time. Continue Reading
-
Tip
15 Nov 2023

How to protect your organization from IoT malware
IoT devices are attractive targets to attackers, but keeping them secure isn't easy. Still, there are steps to take to minimize risk and protect networks from attacks. Continue Reading
-
Tip
15 Nov 2023

Traditional MFA isn't enough, phishing-resistant MFA is key
Not every MFA technique is effective in combating phishing attacks. Enterprises need to consider new approaches to protect end users from fraudulent emails. Continue Reading
-
News
14 Nov 2023

Cryptocurrency wallets might be vulnerable to 'Randstorm' flaw
Cryptocurrency recovery company Unciphered discovered a vulnerability in a JavaScript Bitcoin library that could jeopardize private keys. Continue Reading
-
News
13 Nov 2023

LockBit ransomware gang claims it leaked stolen Boeing data
Boeing confirmed that it experienced a cybersecurity incident following LockBit's claims, but the aircraft manufacturer has not directly confirmed a ransomware attack. Continue Reading
-
News
09 Nov 2023

Lace Tempest exploits SysAid zero-day vulnerability
SysAid urged users to patch a zero-day vulnerability in its on-premises software, which is being exploited by the threat actor behind the MoveIt Transfer ransomware attacks. Continue Reading
-
News
08 Nov 2023

FBI: Ransomware actors hacking casinos via third parties
A new Private Industry Notification focuses on ransomware trends involving attacks against casinos as well as a callback phishing campaign perpetrated by the Luna Moth gang. Continue Reading
-
News
08 Nov 2023

Atlassian Confluence vulnerability under widespread attack
Atlassian's Confluence Data Center and Server products are under attack again as reports of widespread exploitation roll in just days after CVE-2023-22518 was publicly disclosed. Continue Reading
-
News
07 Nov 2023

Microsoft, ZDI disagree over Exchange zero-day flaws
Microsoft said it had previously fixed one of the flaws and that the others did not require a patch. Trend Micro's Zero Day Initiative, however, disagreed with the software giant. Continue Reading
-
Tip
07 Nov 2023

7 useful hardware pen testing tools
Penetration testers use a variety of hardware to conduct security assessments, including a powerful laptop, Raspberry Pi, Rubber Ducky and more. Continue Reading
-
News
06 Nov 2023

Ransomware continues to rise in October across all sectors
Ransomware disclosures and reports surged last month, leading in some cases to bankruptcy filing, prolonged business disruptions and ambulance diversions for hospitals. Continue Reading
-
Feature
03 Nov 2023

9 secure email gateway options for 2024
Finding the best email security gateway is vital to protect companies from cyber attacks. Here's a look at some current market leaders and their standout features. Continue Reading
-
News
02 Nov 2023

Zscaler finds 117 Microsoft 365 bugs via SketchUp 3D file type
Microsoft published patches to address all 117 Microsoft 365 Apps flaws disclosed Tuesday, and the tech giant has disabled support for SketchUp, or SKP, 3D model files. Continue Reading
-
News
31 Oct 2023

No patches yet for Apple iLeakage side-channel attack
Apple said it is working on more complete fixes for the iLeakage side-channel attack technique, but only one partial mitigation is currently available to macOS customers. Continue Reading
-
Tip
30 Oct 2023

Adversarial machine learning: Threats and countermeasures
As machine learning becomes widespread, threat actors are developing clever attacks to manipulate and exploit ML applications. Review potential threats and how to combat them. Continue Reading
-
Tip
30 Oct 2023

What an email security policy is and how to build one
Companies must have an effective security policy in place to protect email from cybercriminals and employee misuse. Learn how to build one for your company. Continue Reading
-
Tip
27 Oct 2023

How to create a cybersecurity awareness training program
Cybersecurity awareness training often misses the mark, leaving employees undereducated and organizations vulnerable to attack. Here's how to succeed where too many fail. Continue Reading
-
News
26 Oct 2023

NCC Group details 153% spike in September ransomware attacks
NCC Group analysts warned the significant year-over-year increase will likely continue. Organizations may see 4,000 ransomware attacks by the end of 2023. Continue Reading
-
News
24 Oct 2023

Cisco IOS XE instances still under attack, patch now
In the days since Cisco's initial disclosure, the networking giant found a second Cisco IOS XE zero-day as well as new evasion techniques being utilized by threat actors. Continue Reading
-
Tip
23 Oct 2023

12 common types of malware attacks and how to prevent them
The umbrella term malware is one of the greatest cybersecurity threats enterprises face. Learn about 12 common types of malware and how to prevent them. Continue Reading
-
Feature
23 Oct 2023

Top 10 tips for employees to prevent phishing attacks
Share this list of phishing techniques, detection and prevention tips, and best practices to help employees avoid falling victim to phishing schemes. Continue Reading
-
News
19 Oct 2023

CISA, NSA, FBI publish phishing guidance
In its guidance, CISA focused on two primary goals of phishing attacks: obtaining login credentials, often via social engineering, and installing malware on target systems. Continue Reading
-
Tip
19 Oct 2023

Top 15 email security best practices for 2024
Attackers exploit email every day to break into corporate networks, but the risk can be reduced by adhering to these 15 email security best practices. Continue Reading
-
Tip
18 Oct 2023

Cybersecurity vs. cyber resilience: What's the difference?
Companies need cybersecurity and cyber-resilience strategies to protect against attacks and mitigate damage in the aftermath of a successful data breach. Continue Reading
-
Tip
18 Oct 2023

Use these 6 user authentication types to secure networks
One layer of security that all networks and applications need is authentication. Read up on six authentication types, from 2FA to biometrics to certificates. Continue Reading
-
News
17 Oct 2023

Cisco IOS XE zero-day facing mass exploitation
VulnCheck said its public scanning for CVE-2023-20198 revealed that 'thousands' of internet-facing Cisco IOS XE systems have been compromised with malicious implants. Continue Reading
-
Tip
17 Oct 2023

Allowlisting vs. blocklisting: Benefits and challenges
Allowlisting and blocklisting are key components of access control. Learn the benefits and challenges of each approach and why a combination of the two is often the best strategy. Continue Reading
-
News
16 Oct 2023

Cisco working on fix for critical IOS XE zero-day
Cisco designated the bug, CVE-2023-20198, with a CVSS score of 10 and said it was working on a patch, but advised customers to apply mitigations in the meantime. Continue Reading
-
News
13 Oct 2023

Ransomware gang targets critical Progress WS_FTP Server bug
The vulnerability used in the failed ransomware attack, CVE-2023-40044, is a .NET deserialization vulnerability in Progress Software's WS_FTP Server with a CVSS score of 10. Continue Reading
-
Answer
13 Oct 2023

What are the most important email security protocols?
Email was designed without security considerations. Email security protocols, including SMPTS, SPF and S/MIME, add mechanisms to keep messaging safe from threats. Continue Reading
-
Feature
10 Oct 2023

Security posture management a huge challenge for IT pros
Enterprise Strategy Group's John Oltsik explains why executing security hygiene and posture management at scale remains an uphill battle for organizations, despite automation. Continue Reading
-
News
04 Oct 2023

Critical Atlassian Confluence zero-day flaw under attack
Collaboration software vendor Atlassian urged customers with affected versions of Confluence Data Center and Server to apply patches for CVE-2023-22515 immediately. Continue Reading
-
News
03 Oct 2023

Spyware vendor exploiting kernel flaw in Arm Mali GPU drivers
Arm Mali GPUs affected by CVE-2023-4211, which was discovered by Google researchers, include a wide range of Android phones as well as ChromeOS devices such as Chromebooks. Continue Reading
-
News
03 Oct 2023

Ransomware disrupts hospitality, healthcare in September
Ransomware disclosures and reports last month were headlined by attacks on MGM Resorts and Caesars Entertainment, which proved costly to the Las Vegas hospitality giants. Continue Reading
-
News
02 Oct 2023

Openwall patches 3 of 6 Exim zero-day flaws
The Openwall Project urged users to upgrade to the latest version of Exim, but there have been timely patching struggles with the message transfer agent software in the past. Continue Reading
-
Tip
29 Sep 2023

5 common browser attacks and how to prevent them
Browsers are critical components of any organization, especially with the rise of web apps. Security teams and users must, therefore, know how to avoid common browser attacks. Continue Reading
-
News
28 Sep 2023

US, Japan warn China-linked 'BlackTech' targeting routers
CISA said BlackTech has targeted Cisco and other router makers by using a variety of tools and techniques to modify and even replace devices' firmware. Continue Reading
-
News
28 Sep 2023

Cisco patches zero-day vulnerability under attack
Cisco said its Advanced Security Initiatives Group discovered the zero-day flaw while investigating attempted attacks on the vendor's Group Encrypted Transport VPN feature. Continue Reading
-
News
26 Sep 2023

Clop MoveIt Transfer attacks affect over 2,000 organizations
According to research by security vendor Emsisoft, 2,095 organizations and 62,054,613 individuals have been affected by the Clop gang's attacks on MoveIt Transfer customers. Continue Reading
-
News
26 Sep 2023

MSP shares details of Kaseya VSA ransomware attack, recovery
Progressive Computing was one of 60 victims of the Kaseya VSA ransomware attack in 2021. Now, a co-founder tells the story of discovery and recovery. Continue Reading
-
News
22 Sep 2023

Apple issues emergency patches for 3 zero-day bugs
Apple said CVE-2023-41992, CVE-2023-41991 and CVE-2023-41993 -- all reported by Citizen Lab and Google researchers -- might have been exploited against versions of iOS before 16.7. Continue Reading
-
News
20 Sep 2023

Okta: Caesars, MGM hacked in social engineering campaign
Identity management vendor Okta had previously disclosed that four unnamed customers had fallen victim to a social engineering campaign that affected victims' MFA protections. Continue Reading
-
Tip
20 Sep 2023

How to train employees to avoid ransomware
Do your employees know what to do if ransomware strikes? As your organization's first line of defense, they should receive regular trainings on ransomware prevention and detection. Continue Reading
-
Podcast
19 Sep 2023

Risk & Repeat: MGM, Caesars casino hacks disrupt Las Vegas
This podcast episode compares the cyber attacks suffered by casino giants MGM Resorts and Caesars Entertainment in recent weeks and the fallout from them. Continue Reading
-
Tip
19 Sep 2023

How to remove ransomware, step by step
Prevention is key when it comes to ransomware infections. But there are ways to recover data if a device is compromised. Uncover four key steps to ransomware removal. Continue Reading
-
Answer
19 Sep 2023

What is extortionware? How does it differ from ransomware?
Prevention is the only line of defense against an extortionware attack. Learn how extortionware works and why it can be more damaging than ransomware. Continue Reading
-
News
19 Sep 2023

Veeam leads funding round for SaaS backup provider Alcion
Analysts say that while both Alcion and Veeam offer Microsoft 365 backup, there is enough difference in the products and enough need in the data protection market. Continue Reading
-
Tip
14 Sep 2023

How CIOs can build cybersecurity teamwork across leadership
Cross-departmental relationships are key to long-term business success. Discover why CIOs must focus on teamwork with these three C-suite roles for highly effective cybersecurity. Continue Reading
-
News
13 Sep 2023

Browser companies patch critical zero-day vulnerability
While attack details remain unknown, Chrome, Edge and Firefox users are being urged to update their browsers as an exploit for CVE-2023-4863 lurks in the wild. Continue Reading
-
Tip
13 Sep 2023

The 10 biggest ransomware attacks in history
From private organizations and manufacturers to healthcare organizations and entire countries, read up on 10 of the most famous ransomware attacks of all time. Continue Reading
-
News
11 Sep 2023

Cisco VPN flaw faces attempted Akira ransomware attacks
Cisco said it became aware of 'attempted exploitation' last month and referenced an Aug. 24 security advisory saying its VPNs were under attack by the Akira ransomware gang. Continue Reading
-
Feature
09 Sep 2023

The ultimate guide to cybersecurity planning for businesses
This in-depth cybersecurity planning guide provides information and advice to help organizations develop a successful strategy to protect their IT systems from attacks. Continue Reading
-
Tip
08 Sep 2023

6 stages of the ransomware lifecycle
Know thy enemy. By understanding the nuances of the ransomware lifecycle, enterprise security teams can best protect their organizations from attacks. Continue Reading
-
Tip
06 Sep 2023
How to prevent ransomware in 6 steps
Ransomware can cost companies billions in damage. Incorporate these ransomware prevention best practices, from defense in depth to patch management, to keep attackers out. Continue Reading
-
News
05 Sep 2023

Ransomware attacks on education sector spike in August
While data breach notifications for MoveIt Transfer customers continued to rise, August also saw ransomware ramp up against schools and universities as classes resumed. Continue Reading
-
Feature
31 Aug 2023

Malware vs. ransomware: What's the difference?
Ransomware is a type of malware, or malicious software. While all ransomware is malware, not all malware is ransomware. Continue Reading
-
Tip
31 Aug 2023

How to recover from a ransomware attack
With a ransomware recovery plan, organizations can act quickly to prevent data loss without descending into chaos. Learn the six steps to incorporate into your plan. Continue Reading
-
Feature
31 Aug 2023

Types of ransomware and a timeline of attack examples
There are eight main types of ransomware but hundreds of examples of ransomware strains. Learn how the ransomware types work, and review notable ransomware attacks and variants. Continue Reading
-
News
30 Aug 2023

FBI, Justice Department dismantle Qakbot malware
The FBI operation, one of the largest U.S.-led botnet disruption efforts ever, included international partners such as France, Germany, the Netherlands and the United Kingdom. Continue Reading
-
Guest Post
30 Aug 2023

SEC cyber attack regulations prompt 10 questions for CISOs
New SEC regulations governing the disclosure of cyber attacks by public companies lead to 10 questions board members should ask their CISOs about managing cyber-risk. Continue Reading
-
News
29 Aug 2023

Microsoft Teams attack exposes collab platform security gaps
Criminal and state-sponsored hackers are ramping up cyberattacks on instant messaging platforms and other workplace collaboration tools. Meanwhile, enterprises' readiness lags. Continue Reading
-
News
29 Aug 2023

Mandiant reveals new backdoors used in Barracuda ESG attacks
Further investigations show threat actors were prepared for Barracuda Networks' remediation efforts, including an action notice to replace all compromised devices. Continue Reading
-
Tip
28 Aug 2023

Enterprise dark web monitoring: Why it's worth the investment
Getting an early warning that your data has been compromised is a key benefit of dark web monitoring, but there are many more. By knowing your enemies, you can better protect your assets. Continue Reading
-
Feature
28 Aug 2023

3 ransomware detection techniques to catch an attack
While prevention is key, it's not enough to protect a company's system from ransomware. Reduce damage from attacks with these three ransomware detection methods. Continue Reading
-
Tip
28 Aug 2023

Should companies make ransomware payments?
Once infected with ransomware, organizations face a major question: to pay or not to pay? Law enforcement recommends against it, but that doesn't stop all companies from paying. Continue Reading
-
News
24 Aug 2023

FBI: Suspected Chinese actors continue Barracuda ESG attacks
The alert comes after Barracuda Networks issued an advisory stating that patches for CVE-2023-2868 were insufficient and all affected ESG devices need to be replaced. Continue Reading
-
News
23 Aug 2023

Sophos: RDP played a part in 95% of attacks in H1 2023
While Sophos observed increasing activity around Active Directory and Remote Desktop Protocol abuse, it recommended simple mitigation steps can limit the attack surface. Continue Reading
-
News
22 Aug 2023

Ivanti issues fix for third zero-day flaw exploited in the wild
CVE-2023-38035 is the latest Ivanti zero-day vulnerability to be exploited in the wild. The vendor has released a series of remediation recommendations. Continue Reading
-
News
17 Aug 2023

CISA, vendors warn Citrix ShareFile flaw under attack
A vulnerability in the managed file transfer product that enterprises use is being actively exploited two months after Citrix released a fix. Continue Reading
-
Podcast
17 Aug 2023

Risk & Repeat: Highlights from Black Hat USA 2023
Black Hat USA 2023 in Las Vegas covered several trends, such as generative AI and cloud security issues, as well as new vulnerabilities, including the Downfall flaw in Intel chips. Continue Reading
-
Feature
16 Aug 2023

How to use dynamic reverse engineering for embedded devices
In this excerpt from 'Practical Hardware Pentesting,' read step-by-step instructions on how to find vulnerabilities on IoT devices using dynamic reverse engineering. Continue Reading
-
Tip
14 Aug 2023

Top 3 ransomware attack vectors and how to avoid them
Protecting your organization against these three common ransomware attack entryways could mean the difference between staying safe or falling victim to a devastating breach. Continue Reading
-
Conference Coverage
11 Aug 2023

The latest from Black Hat USA 2023
Use this guide to Black Hat USA 2023 to keep up on breaking news and trending topics and to read expert insights on one of the world's top cybersecurity conferences. Continue Reading
-
Feature
10 Aug 2023

Why using ransomware negotiation services is worth a try
If stakeholders decide to pay ransom demands, using a ransomware negotiation service could improve the situation's outcome and lower the payout. Continue Reading
-
News
09 Aug 2023

Coalition looks to bridge gap between CISOs, cyber insurance
While carriers and CISOs agree cyber insurance has contributed to better security postures, Coalition said the relationship needs to stronger as threat evolve and intensify. Continue Reading
-
News
09 Aug 2023

Onapsis researchers detail new SAP security threats
At Black Hat 2023, Onapsis researchers demonstrated how attackers could chain a series of SAP vulnerabilities impacting the P4 protocol to gain root access to a target network. Continue Reading
-
Answer
09 Aug 2023

Best practices for reporting ransomware attacks
Organizations must decide whether to report ransomware incidents to the authorities and disclose them to the public. Experts weigh in on the options and best practices. Continue Reading
-
News
08 Aug 2023

Google unveils 'Downfall' attacks, vulnerability in Intel chips
Google researcher Daniel Moghimi first reported CVE-2022-40982 and the resulting data leak attacks to Intel in August 2022, but it's taken nearly 12 months to disclose the flaw. Continue Reading
-
Tip
04 Aug 2023

8 vulnerability management tools to consider in 2023
Vulnerability management tools help organizations identify and remediate system and application weaknesses and more. Choose your tool -- or tools -- carefully. Continue Reading
-
News
03 Aug 2023

MoveIt Transfer attacks dominate July ransomware disclosures
Traditional ransomware attacks took a back seat last month, as Clop operators continued to claim victims from the zero-day attacks on MoveIt Transfer customers. Continue Reading
-
Podcast
03 Aug 2023

Risk & Repeat: Microsoft takes heat over Storm-0558 attacks
The Storm-0558 attacks have raised questions about Microsoft's response to a cloud flaw and a stolen MSA key that was used to compromise customer email accounts. Continue Reading
-
News
31 Jul 2023

CISA details backdoor malware used in Barracuda ESG attacks
CISA said Friday that 'Submarine' is a novel persistent backdoor used in attacks against Barracuda Email Security Gateway appliances vulnerable to CVE-2023-2868. Continue Reading
-
Opinion
31 Jul 2023

Lenovo's latest heavy on flash, security for enterprise storage
Lenovo's concentration on QLC flash, hybrid cloud and ransomware protection in its latest hardware and software offerings should aid enterprise buyers. Continue Reading
-
News
27 Jul 2023

Google: 41 zero-day vulnerabilities exploited in 2022
While attackers increasingly exploited zero-day flaws last year, one of the most notable findings from the report emphasized how inadequate patches led to new variants. Continue Reading
-
Tip
26 Jul 2023

How to avoid LinkedIn phishing attacks in the enterprise
Organizations and users need to be vigilant about spotting LinkedIn phishing attacks by bad actors on the large business social media platform. Learn how to foil the attempts. Continue Reading
-
News
25 Jul 2023

Ivanti EPMM zero-day vulnerability exploited in wild
A zero-day authentication bypass vulnerability in Ivanti Endpoint Manager Mobile was exploited in a cyber attack against a Norwegian government agency. Continue Reading
-
News
24 Jul 2023

Coveware: Rate of victims paying ransom continues to plummet
Incident response firm Coveware said 34% of ransomware victims paid the ransom in Q2 2023, a sharp decline from last quarter and an enormous decline from 2020 and 2019. Continue Reading
-
Opinion
24 Jul 2023

IBM FlashSystem 5045 aids access to storage cyber resilience
As ransomware and other cyber attacks persist, enterprises should prioritize cyber resilience. IBM's FlashSystem 5045 improves accessibility for that protection. Continue Reading
-
Tip
20 Jul 2023

API keys: Weaknesses and security best practices
API keys are not a replacement for API security. They only offer a first step in authentication -- and they require additional security measures to keep them protected. Continue Reading
-
Podcast
20 Jul 2023

Risk & Repeat: Are data extortion attacks ransomware?
Ransomware gangs are focusing more on data theft and extortion, while skipping the encryption of networks. But should these attacks still be considered ransomware? Continue Reading
-
News
19 Jul 2023

Citrix NetScaler ADC and Gateway flaw exploited in the wild
Critical remote code execution flaw CVE-2023-3519 was one of three vulnerabilities in Citrix's NetScaler ADC and Gateway. Customers are urged to patch their instances. Continue Reading
-
News
18 Jul 2023

Multiple Adobe ColdFusion flaws exploited in the wild
One of the Adobe ColdFusion flaws exploited in the wild, CVE-2023-38203, was a zero-day bug that security vendor Project Discovery inadvertently published. Continue Reading
-
Feature
18 Jul 2023

Ransomware case study: Recovery can be painful
In ransomware attacks, backups can save the day and the data. Even so, recovery can still be expensive and painful, depending on the approach. Learn more in this case study. Continue Reading